04 Apr Phishing for your data
Phishing is rife, and they’re only getting smarter
Hackers are beavering away via a number of routes to get access to your personal data. Email is by far one of the simplest means of access for cybercriminals into a computer network.
You can of course filter your emails, but only to a point – otherwise, you’d never receive any ever again!
Phishing is the act of trying to trick an email recipient into inadvertently sharing their data. The tactics by which these sorts of ‘cyber attacks’ are conducted are getting smarter all the time.
In turn, users need to get sharper – knowing what to look out for when receiving emails. This article from Puzzle Technology aims to offer some helpful advice so that businesses can protect themselves from Phishing scams.
Phishing – How do they do it?
Faking email addresses as though they were sent from someone else’s mailbox is surprisingly simple to do.
The email itself, (in most cases), isn’t actually dangerous. You can simply delete it.
The exposure comes from clicking a link embedded within or opening the attachment from the email. From this link or attached file, a virus, malware or malicious software will download and install itself to your computer – often without the user being aware anything has happened at all.
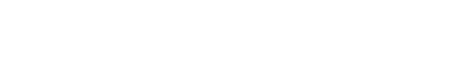
See an example case below, (with the victim sender’s details omitted), to which we refer to through this blog article.
What does it look like in my inbox?
The emails are very cleverly masked. They will appear from a legitimate person, with a real email address and could even contain an email signature & disclaimer from a real business. The contact may well be known to you and the sort of content contained within the email, may be something that you would generally expect to see from that person. Lulling you as the recipient into a false sense of security.
The email, however, is most likely to contain an attachment or a link, which is the lure to draw you toward their means by which they can enter your PC & steal your data. This hopefully would differ from the sort of communication you would normally expect to receive (if at all) from this particular email address – helping it stand out as an email to be wary of.
What can I look out for?
When you receive any email there are a few key things to check, even if you know & trust the sender.
- The sender’s name & email address. Is it someone you know? Could you call them and check they meant to send you this particular email?
- Does the email have an attachment?
If it is a PDF document, there’s a strong chance that you’re safe.
If it is a Word or Excel document, it may well contain a virus hidden in a script that will run automatically once you open the file.
One thing to bear in mind is that you can’t tell from looking at the file whether it is genuine or malicious before you open it. If you do open it and it’s malicious, it’s probably too late.
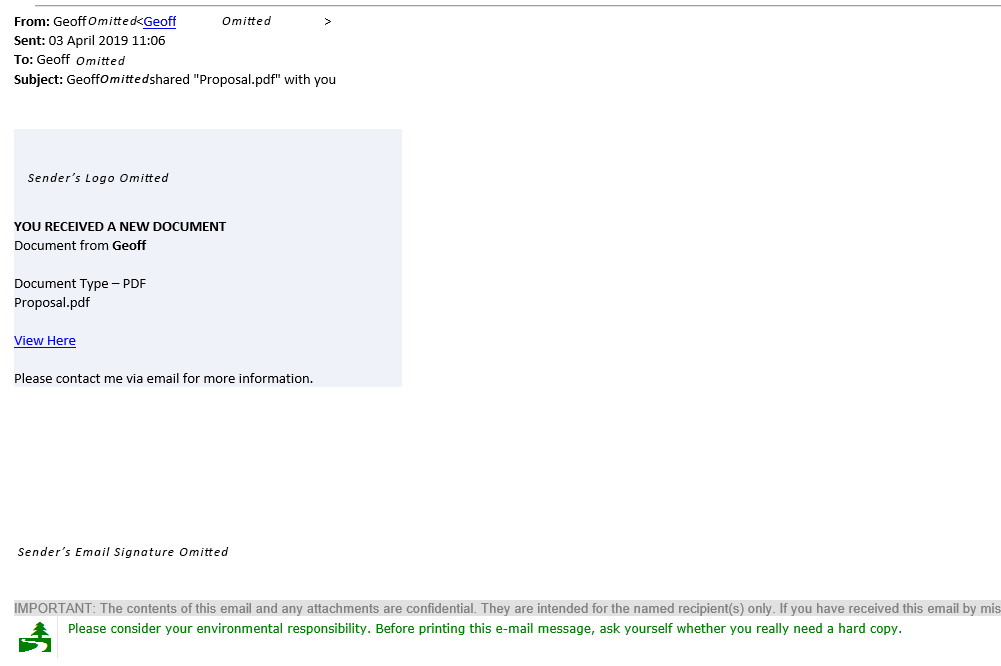
- Does the email contain any links?
Links are far simpler to check. Hover over the link and your computer will show the website destination where the link will actually take you.
If the link appears to be the real website, or where you would expect to land, like in the example below, then it may well be genuine, but that is no guarantee!
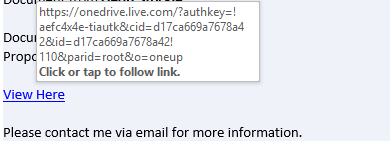
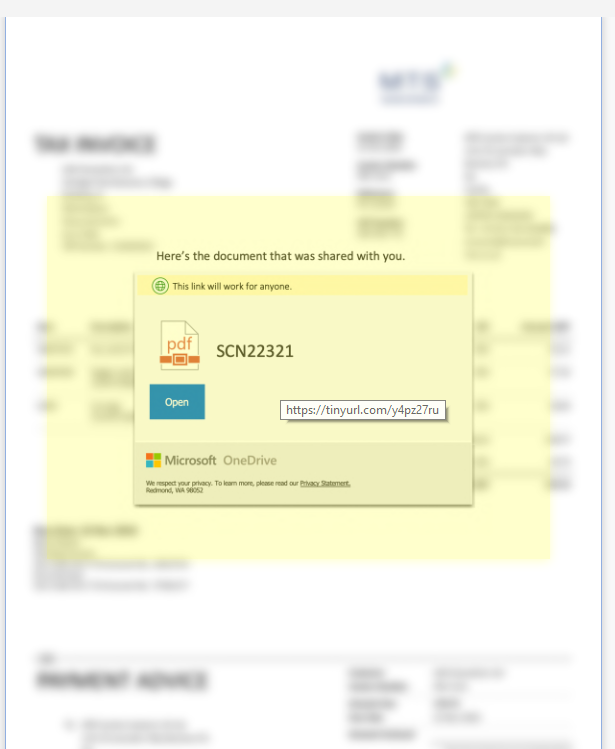
With this example, the link takes you to a file hosted in a Microsoft OneDrive account. The email makes it look like this user did actually want to send you this file, which is stored in a reputable place. If the link appears to be of an untrusted source, it would naturally appear to be more suspicious, but on face-value this particular example link appears to be legitimate.
Clicking the link to visit the website, which appears to be a real Microsoft OneDrive file share, you can see an overview of the document, apparently a PDF.
Upon further inspection, hovering over the preview shows the Microsoft notification box with the “Open” button to infact be faked – it’s just be an image, not a real notification box. Hovering anywhere over the open screen shows the entire image to be hyperlinked to a shortened url, (via tinyurl), cleverly masking a malicious website.
Had the “Open” button been genuine and the document been able to be viewed within the browser it would have likely been entirely legitimate.
However on this example, clicking this link does actually take you through to a virus riddled website, leading to the recipient’s email accounts vulnerable to being hacked & in-turn become a sender out the very same email I received!
In Summary
Be very, very wary. Even if you believe to know the person that sent you the email.
Follow our straight-forward 3-step check list – sender’s name & email address, attachments and links. Checking these three key things before taking any action with the email will help you remain protected.
Want to get the best for your business?
We specialise in learning our clients’ business and best-applying security technology to their needs.
If you would appreciate a free brief discussion about your operational challenges & to explore the threats to your business, please get in touch today – 01480 570339 or drop us a line [email protected]